Someone on Your Team Signed Up for a New SaaS App Today. You Don't Know Which One.
Find shadow apps through OAuth, email, and domain intelligence. Scored by risk, not just existence.
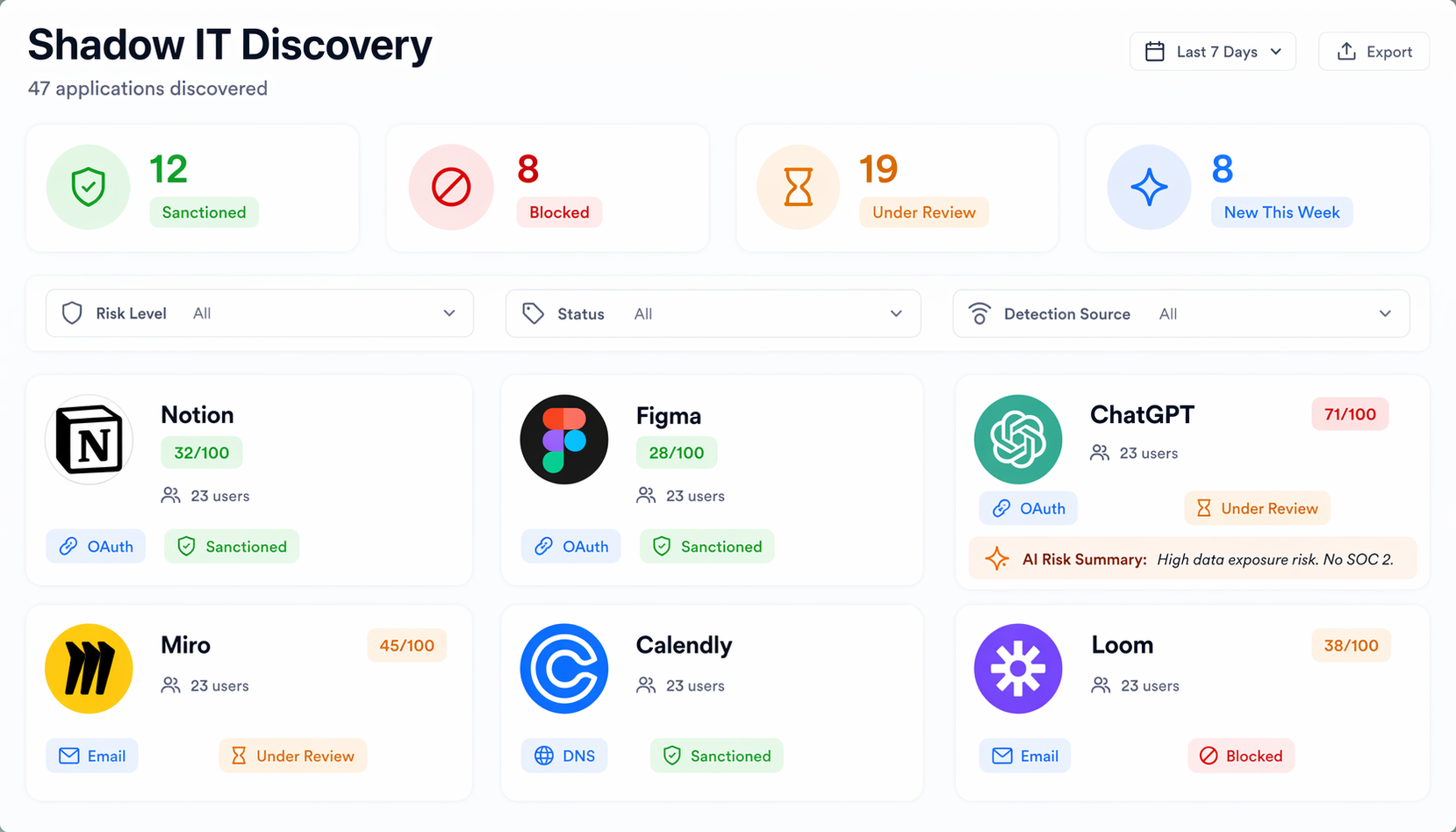
Find shadow apps through OAuth, email, and domain intelligence. Scored by risk, not just existence.
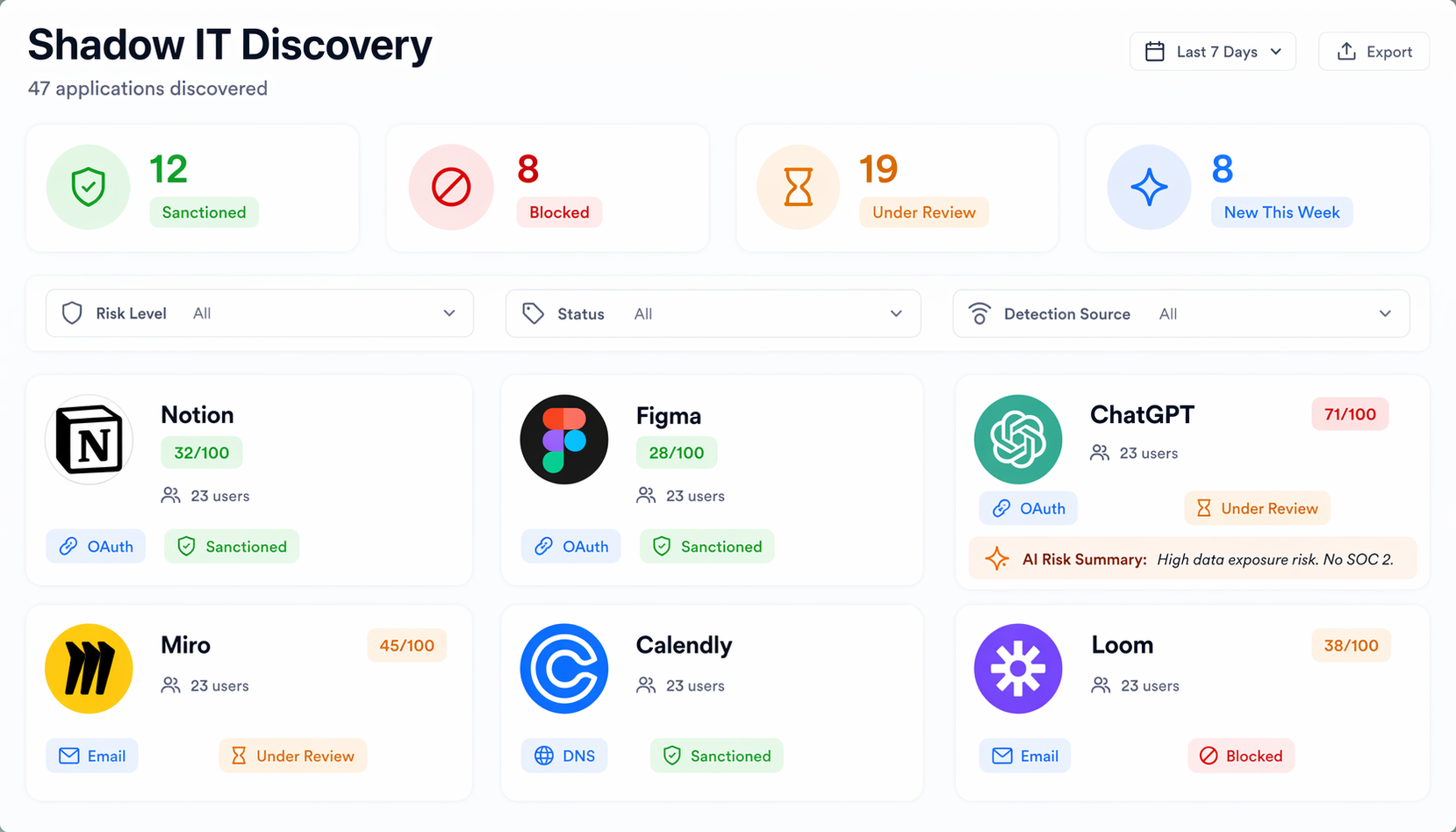
The barrier to adopting a SaaS tool touching company data. No procurement. No security check. You find out during the breach.
Someone clicked "Allow" and gave a random app read access to their entire Google Drive. Hundreds of OAuth grants you've never reviewed.
A list of app names is useless. You need who's using it, what data it touches, and whether it's a real risk. Discovery without context is a bigger spreadsheet.
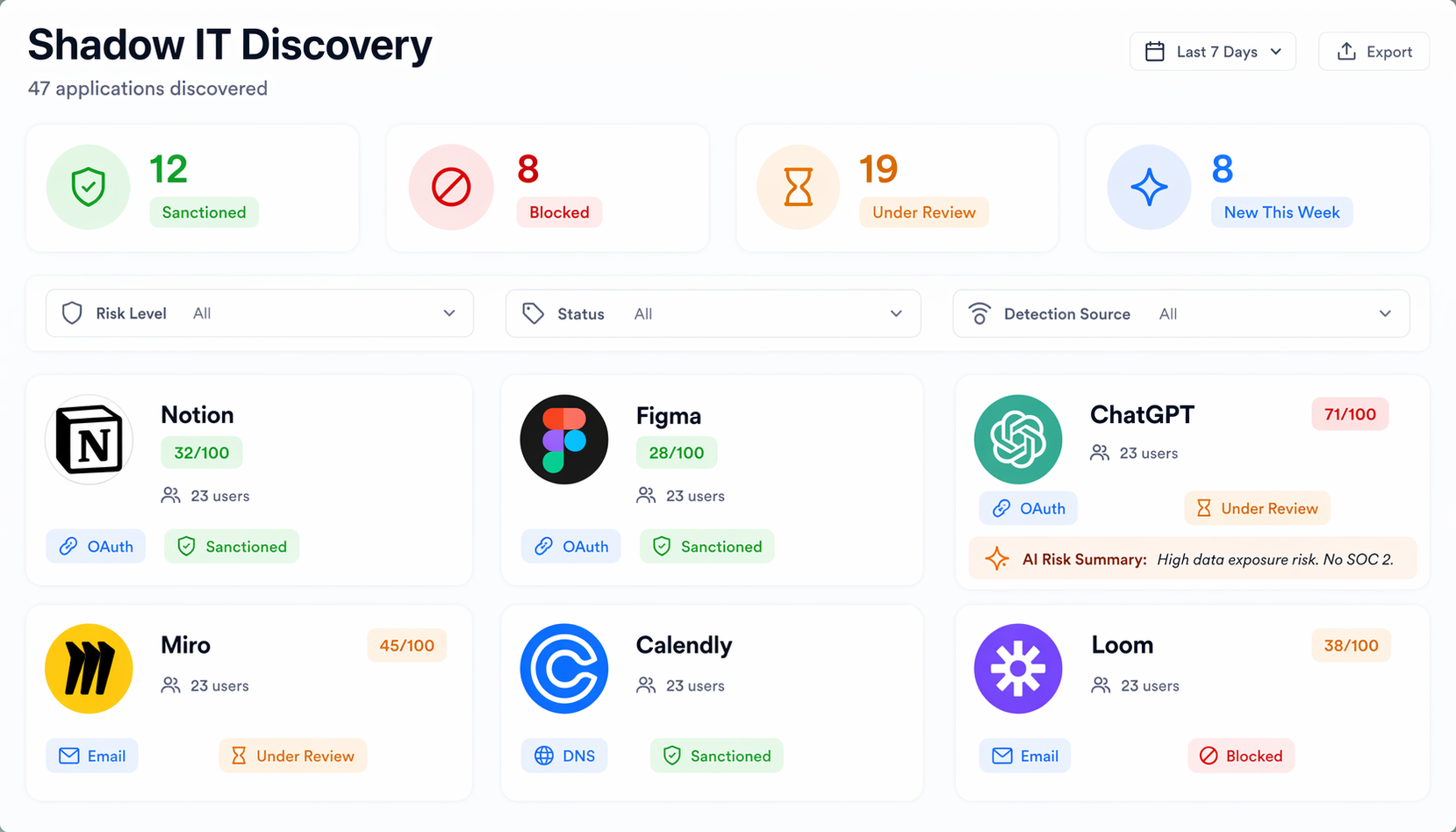

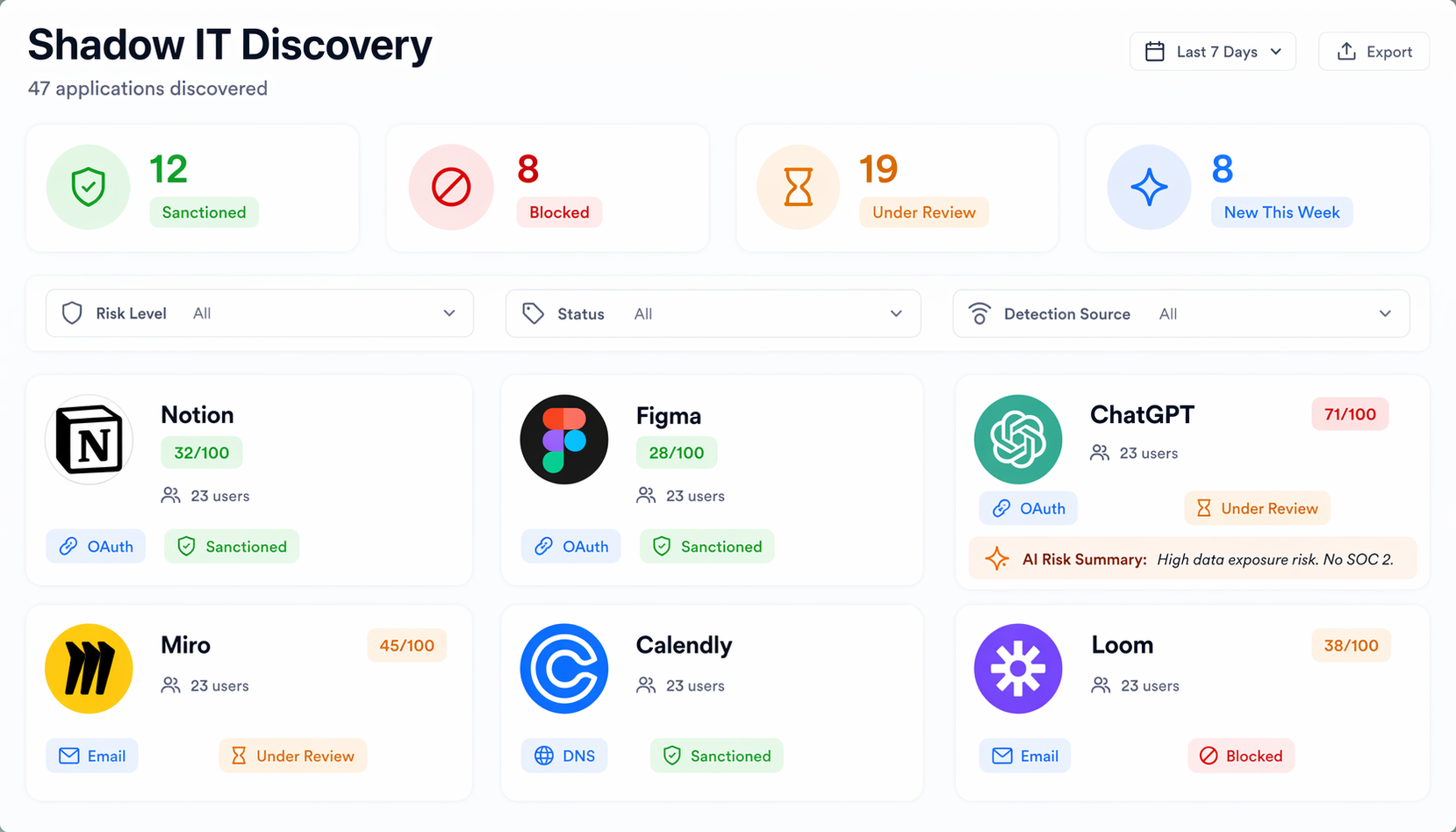

Network traffic analysis for apps that slip past OAuth and email. Expense report mining for SaaS buried in corporate cards. ML risk prediction for shadow apps about to become problems.
OAuth, email, and DNS signals. Risk-scored. No appliances needed.
Every OAuth grant across your tenant. Flag dangerous scopes instantly.
Which shadow apps are SOC 2 compliant? Which store PII? Now you know.
New shadow app Wednesday, you know Thursday. Not next quarter.
Three teams, three project management tools. Find overlap, cut the rest.
Most teams discover 3-5x more apps than they expected. Find out what's actually running in yours.