Your Governance Tool Certifies Access. Who's Watching for the Attack?
100+ detection rules. Correlation engine. Investigation center. What IGA has been missing.
100+ detection rules. Correlation engine. Investigation center. What IGA has been missing.
Your governance tool said "access approved" for an already-compromised account. It certifies permissions. It doesn't notice exfiltration.
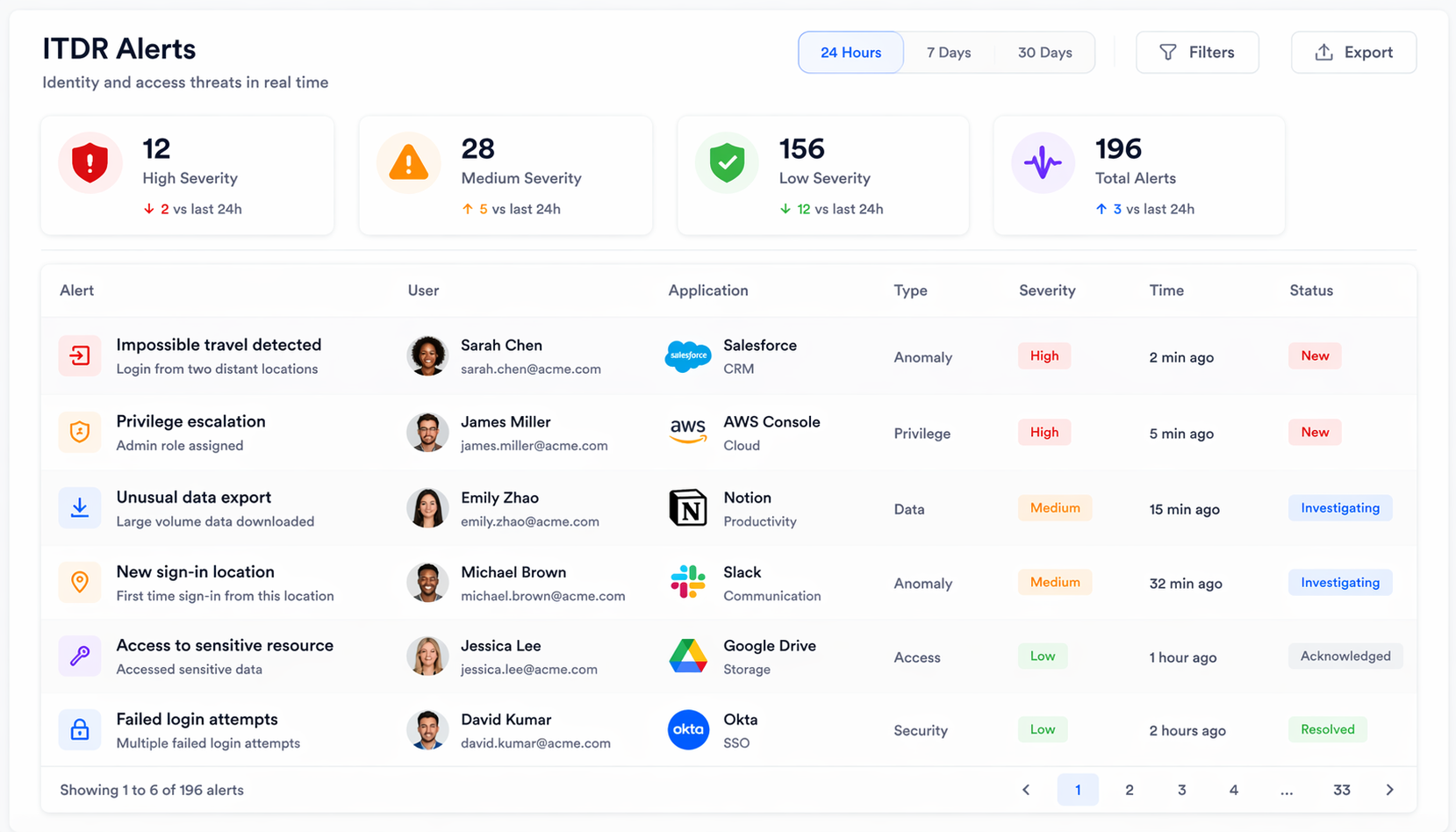
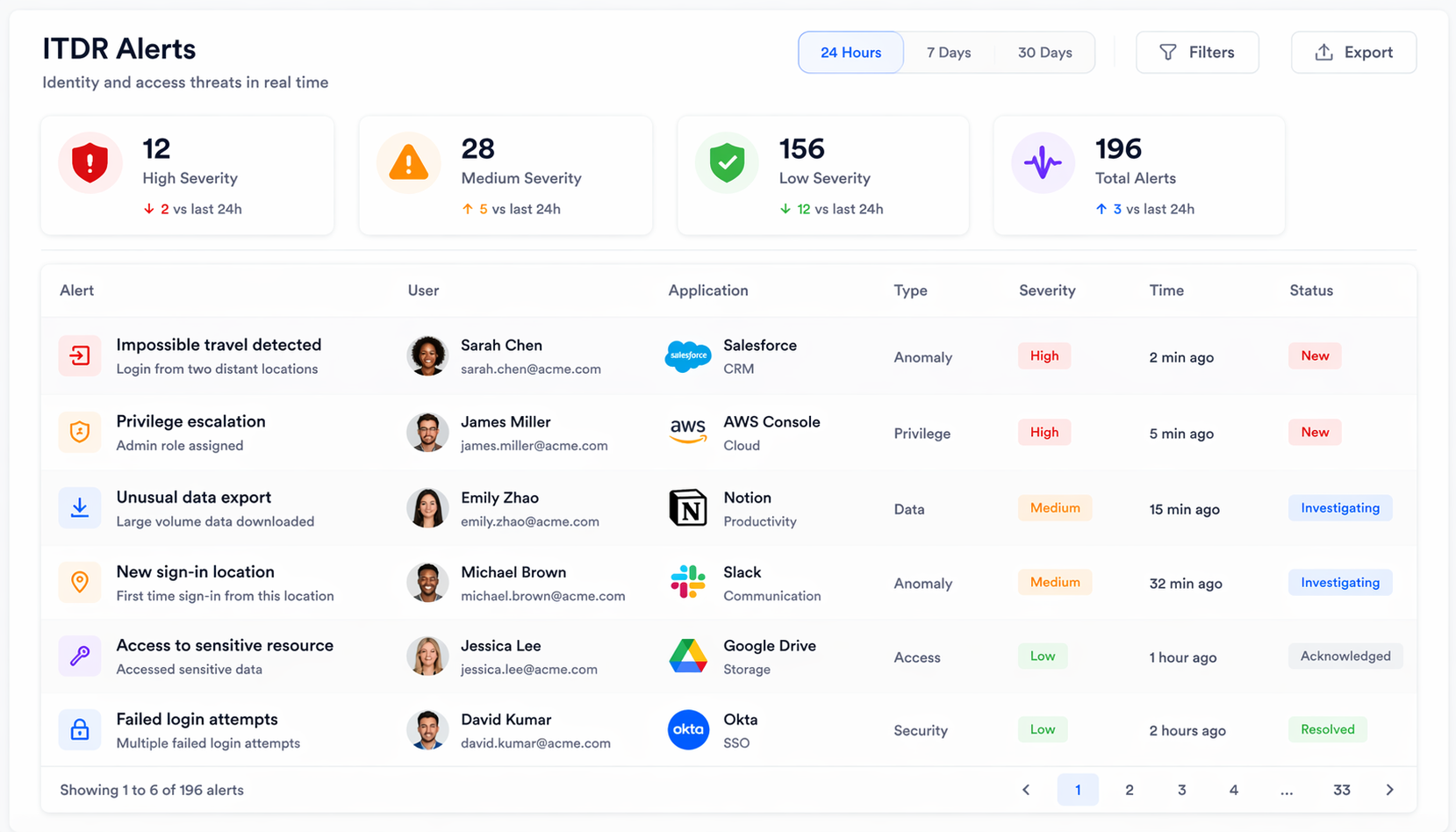
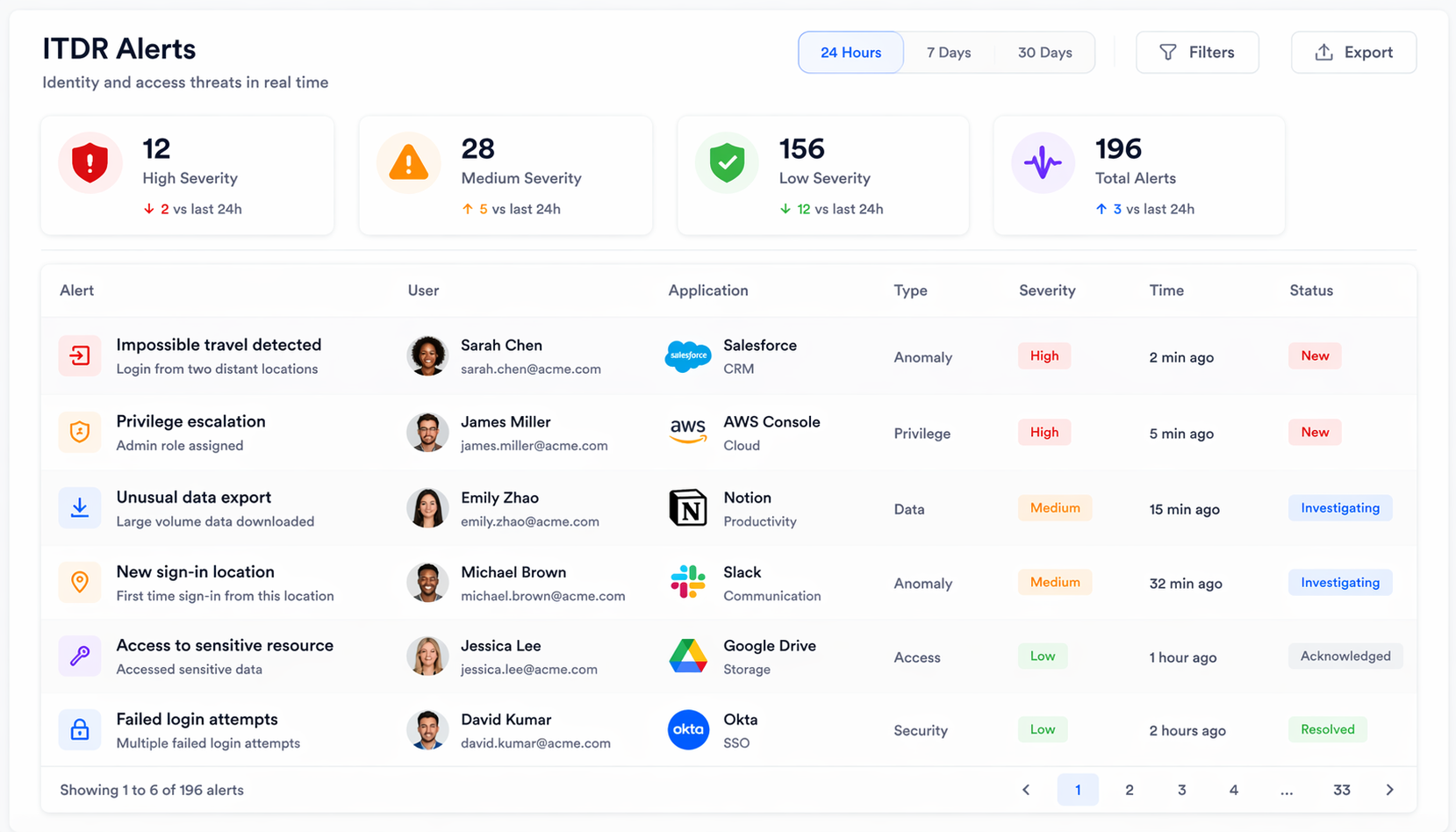
Most are noise. Buried in it: privilege escalation, OAuth grant, data access from a new IP. Without identity correlation, that chain stays invisible.
Over-privileged service principals. Dormant admin accounts. OAuth grants with "read all files" scope. Unlocked doors attackers walk through.



UEBA Behavioral Analytics -- ML baselines per user. When behavior stops looking like theirs, you know. No rule required.
Insider Threat Scoring -- Behavioral anomalies, access patterns, and external indicators fused into one threat score.
Autonomous Response -- Auto-contain compromised accounts and revoke suspicious OAuth grants at machine speed. High-severity actions require a human.
Natural Language Investigation -- "Show me all paths from contractors to production data." Real answers from the identity graph.
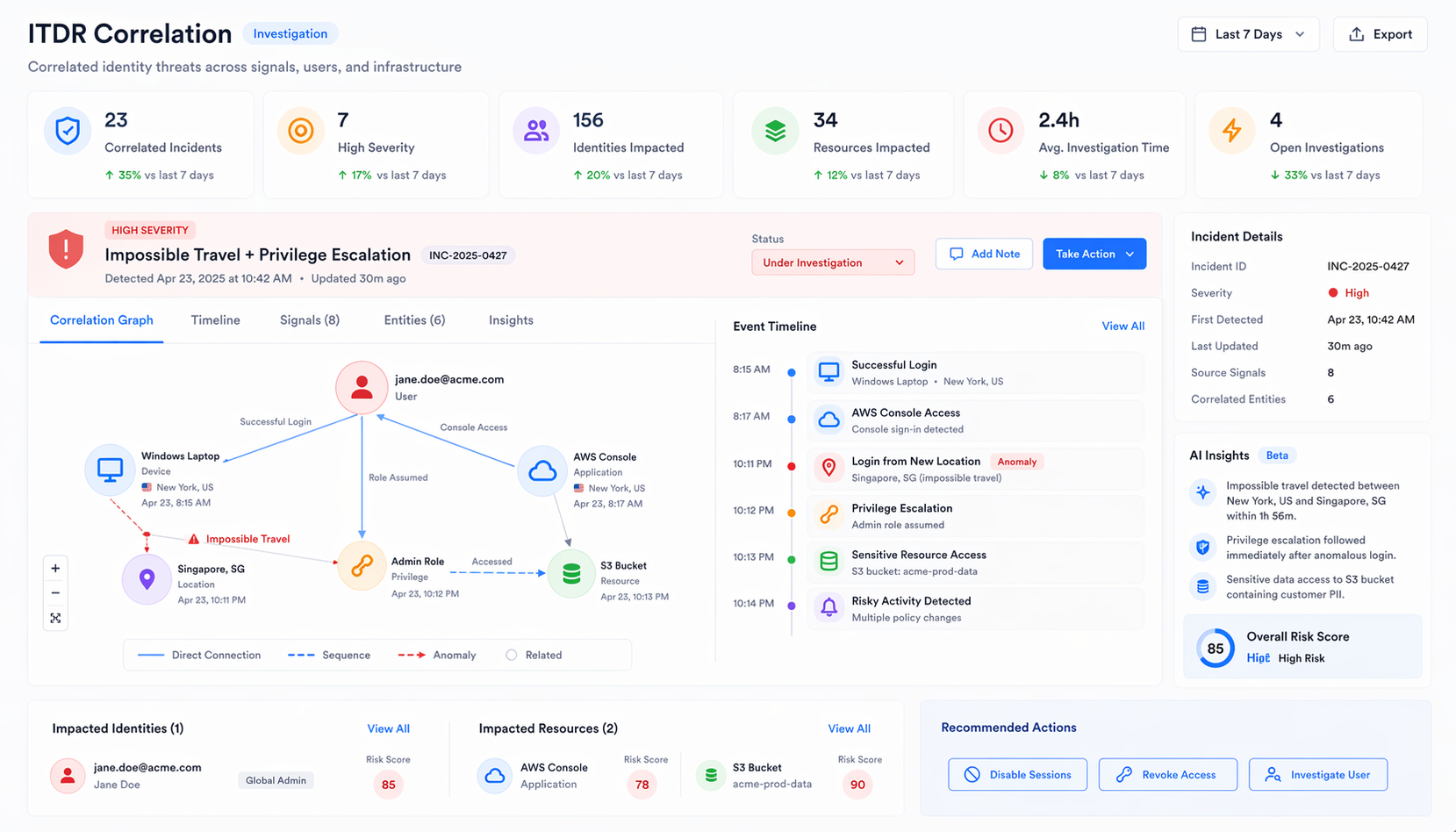
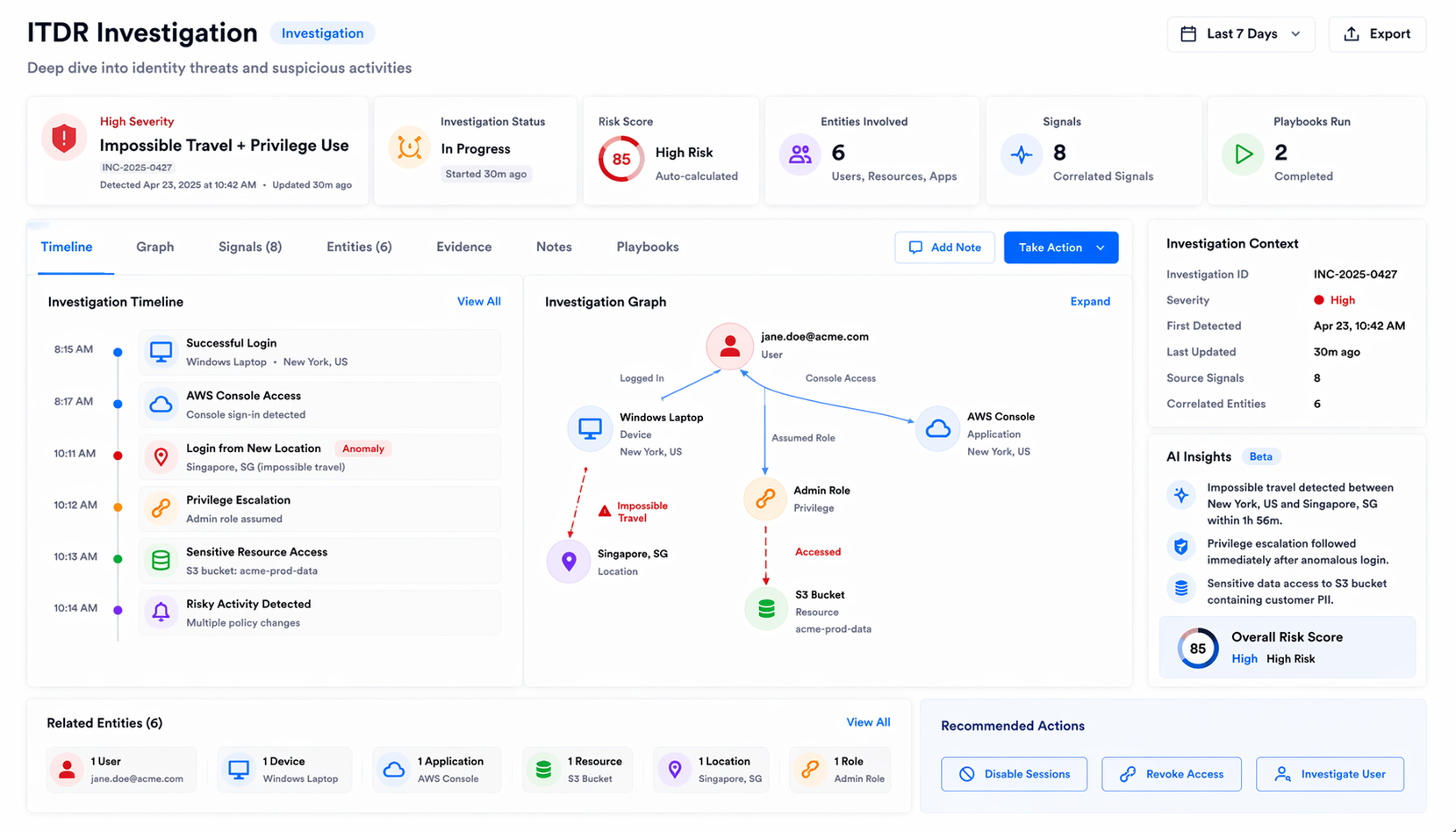
Impossible travel + password change + OAuth grant = one investigation.
Intern got Global Admin via nested group. You know in seconds.
App got "Mail.ReadWrite.All" consent. Flagged before it reads a mailbox.
Service principal with Directory.ReadWrite.All and no owner? Found it.
Credentials in a breach dump. Auto-trigger password reset and investigation.
12 admin accounts dormant 6+ months. Each one a free entry point.
Event timeline, AI summaries, related alerts, team assignment. No context-switching.
EnscureX is the only IGA platform with real-time identity threat detection. See what that looks like.