Governance without threat intel
is just paperwork.
Identity governance meets real-time threat detection. Certify access knowing who's under attack.

Identity governance meets real-time threat detection. Certify access knowing who's under attack.

IGA governs access. SIEM detects threats. Nobody connects the two.
Your governance tool certifies access. It doesn't watch for abuse.
94% still run quarterly reviews on spreadsheets. That's paperwork, not security.
SC Media, 2025 State of IGA Report
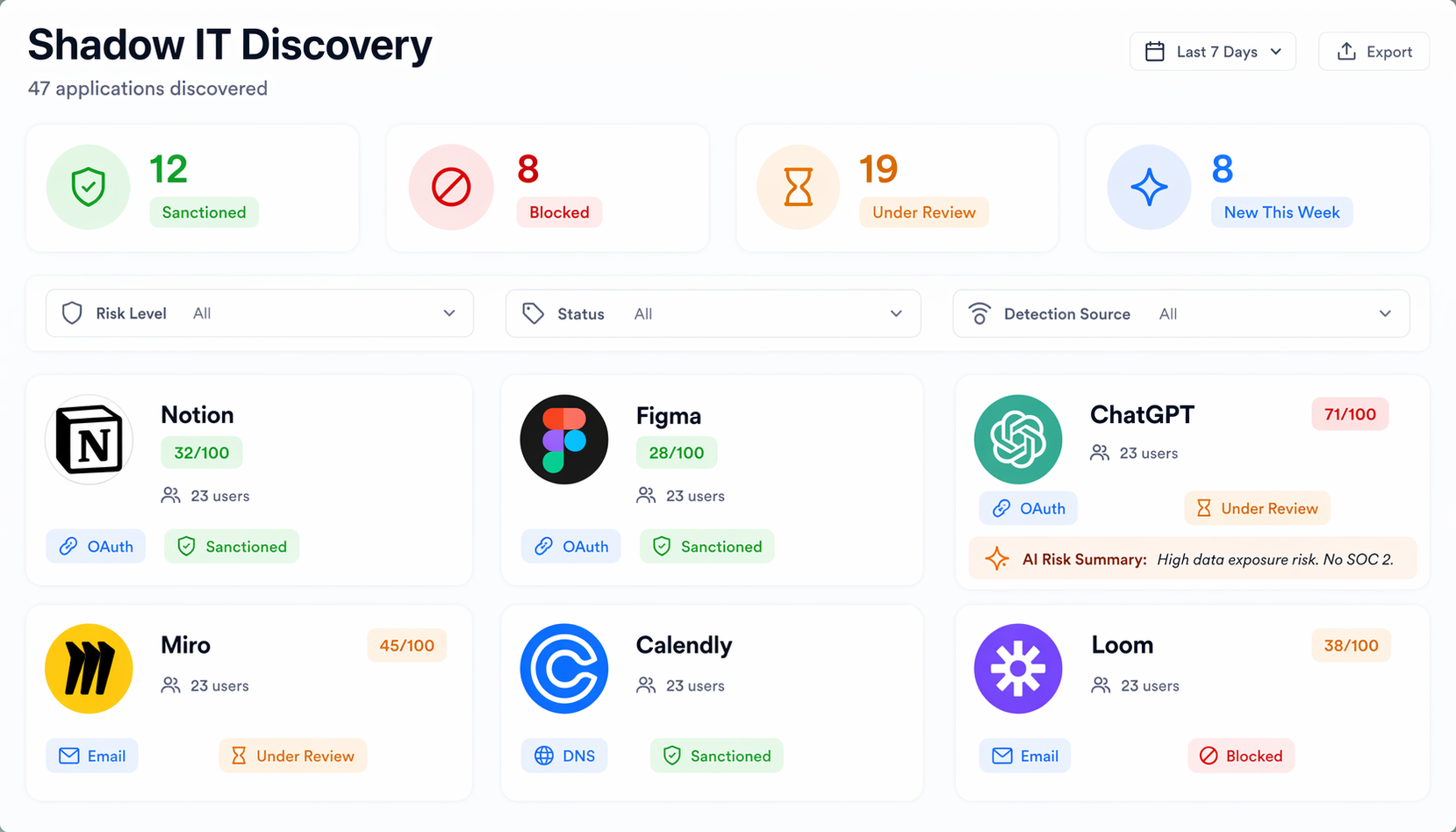
Each app is an attack surface. How many are sanctioned? How many does IT know about?
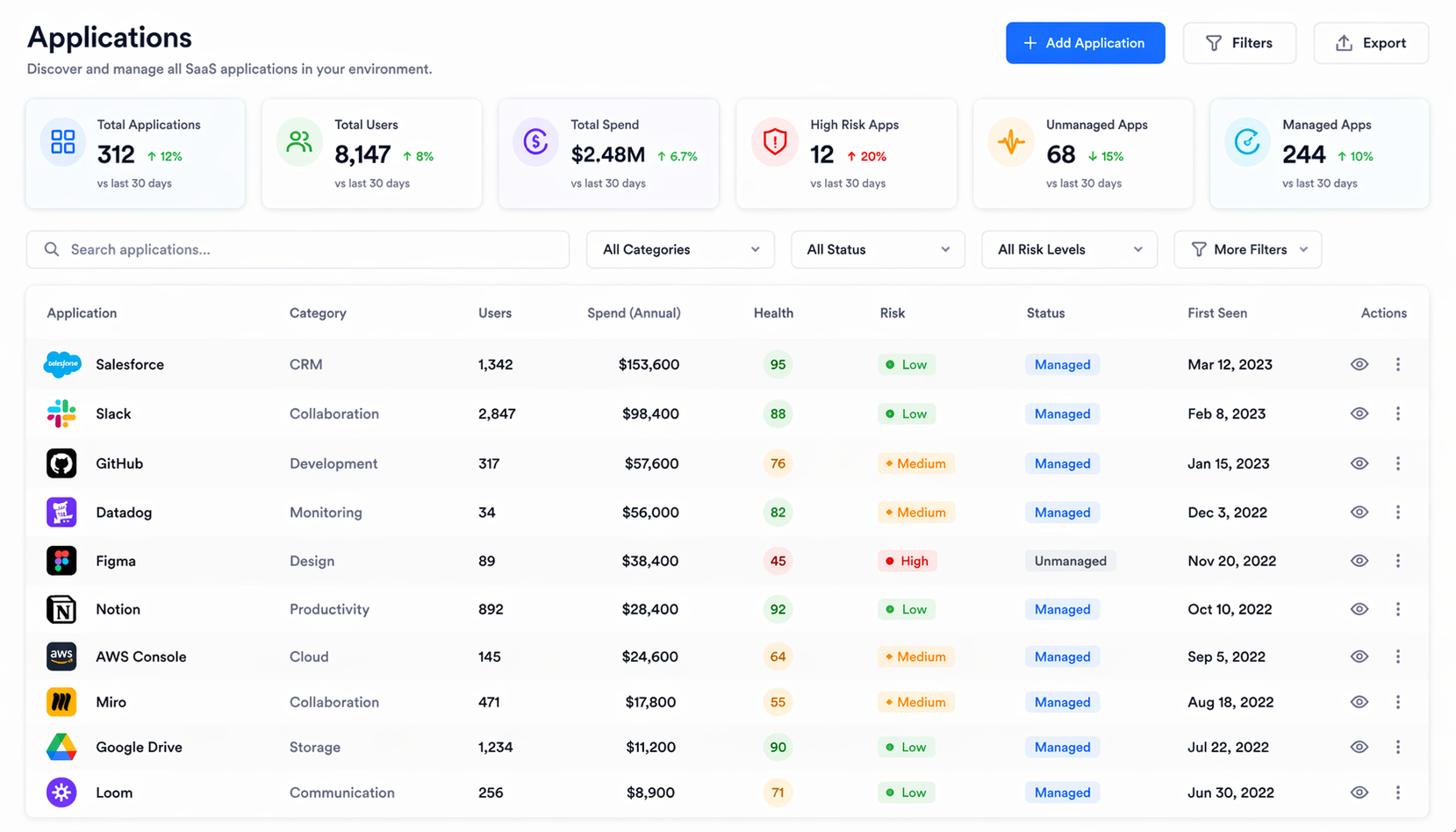
Governance, discovery, SaaS management, and threat detection. Connected at the data layer.
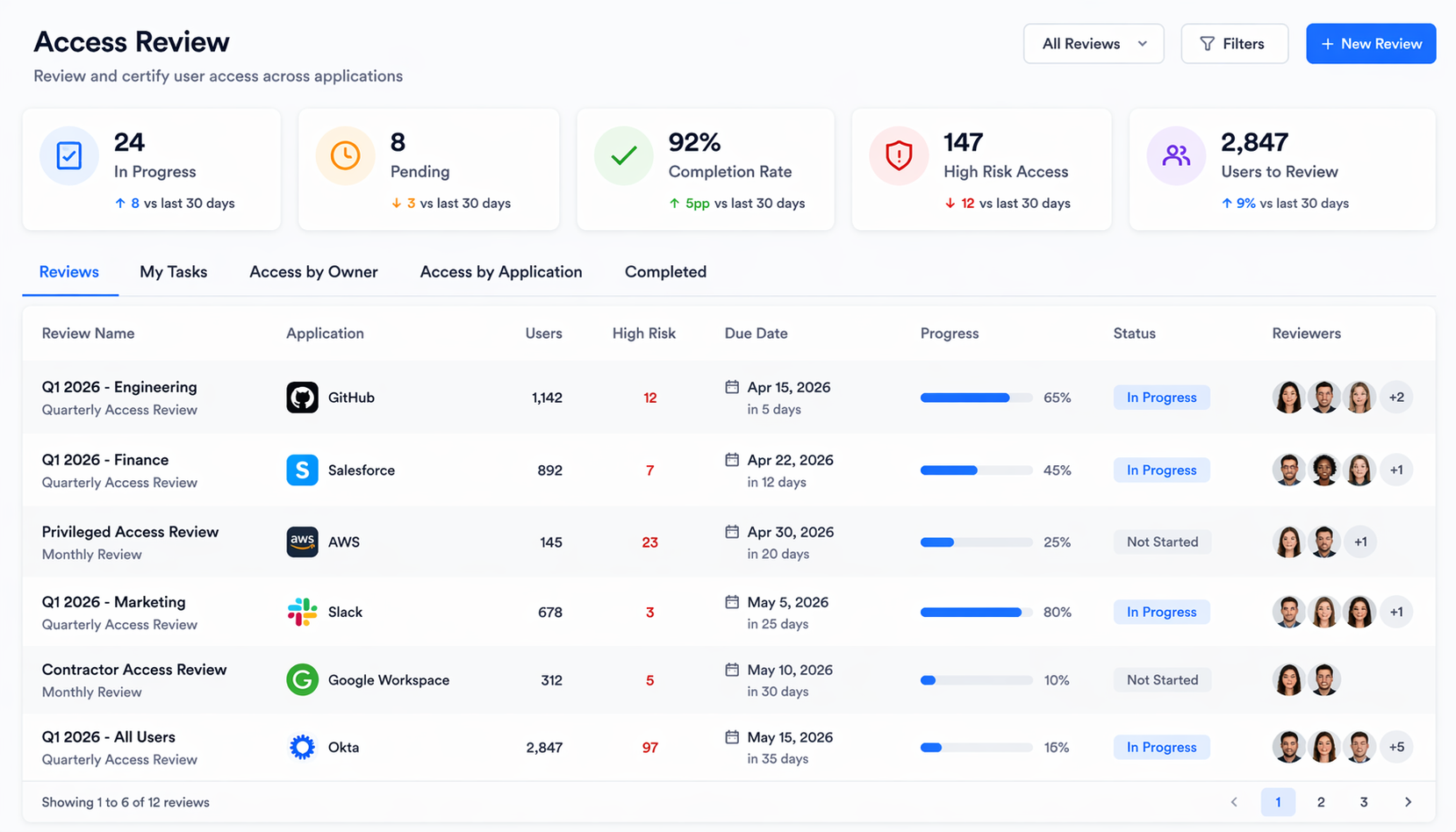
Risk-aware access reviews. Joiner-to-leaver lifecycle automation. Continuous least privilege.
Find every SaaS app in your environment. Multi-signal detection with AI-powered risk scoring.
OAuth risk, security posture, spend trends, and renewal deadlines. Per app.
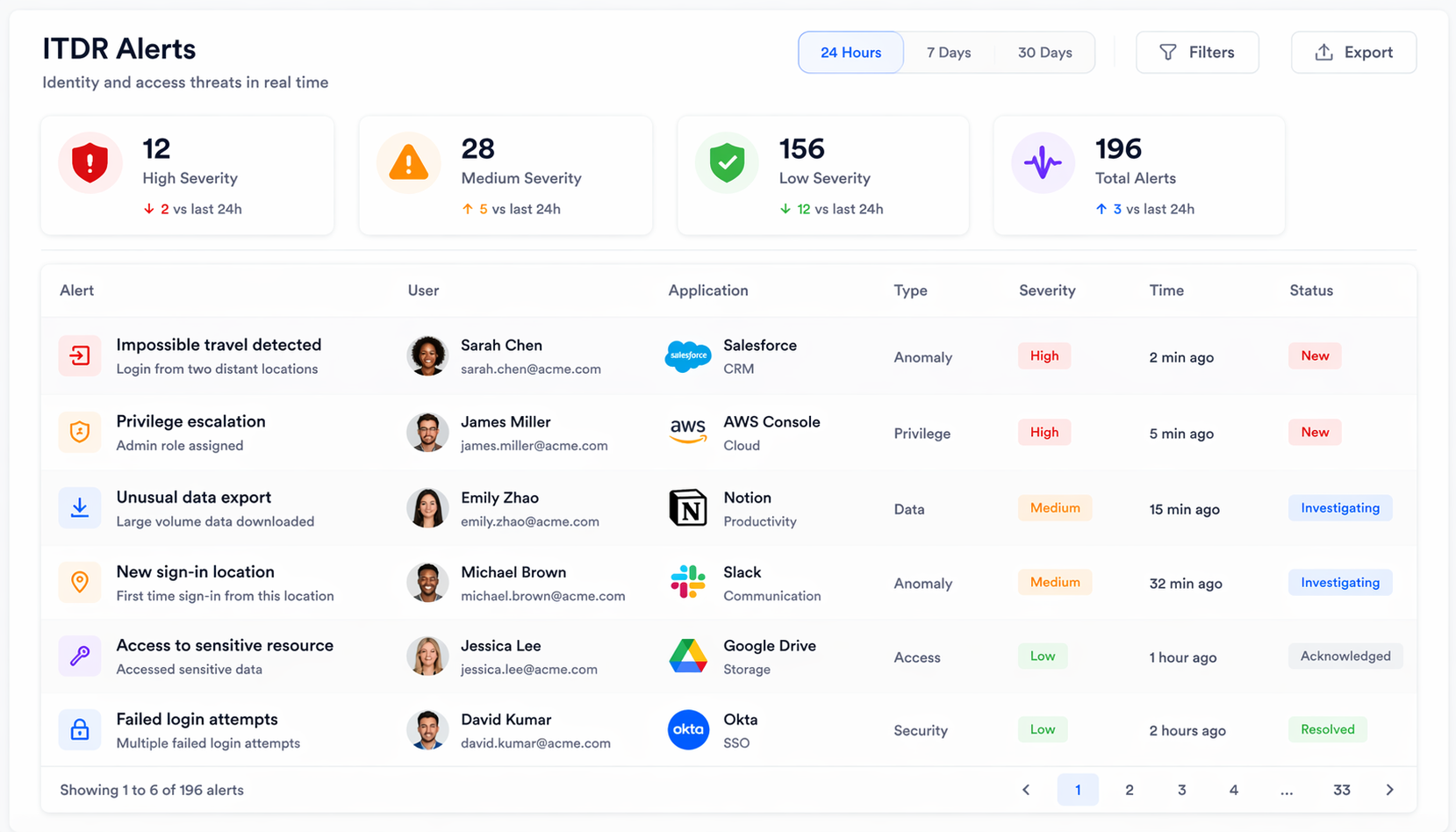
100+ detection rules. Correlation engine linking events into attack chains. No other IGA does this.
What's live. What's next. No vaporware.
Build the platform first. Add intelligence second. An AI agent with bad data is just a faster way to be wrong.
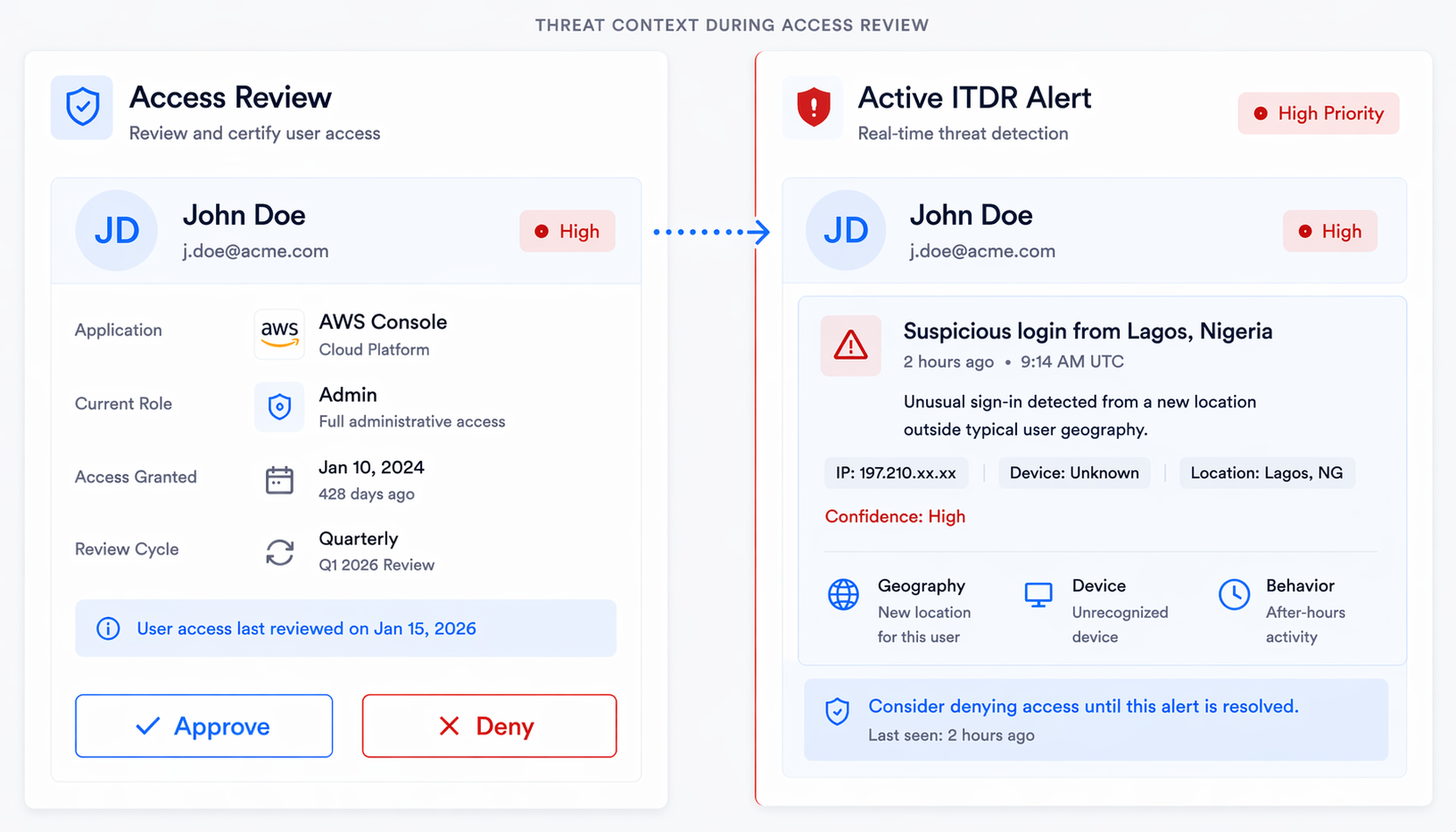
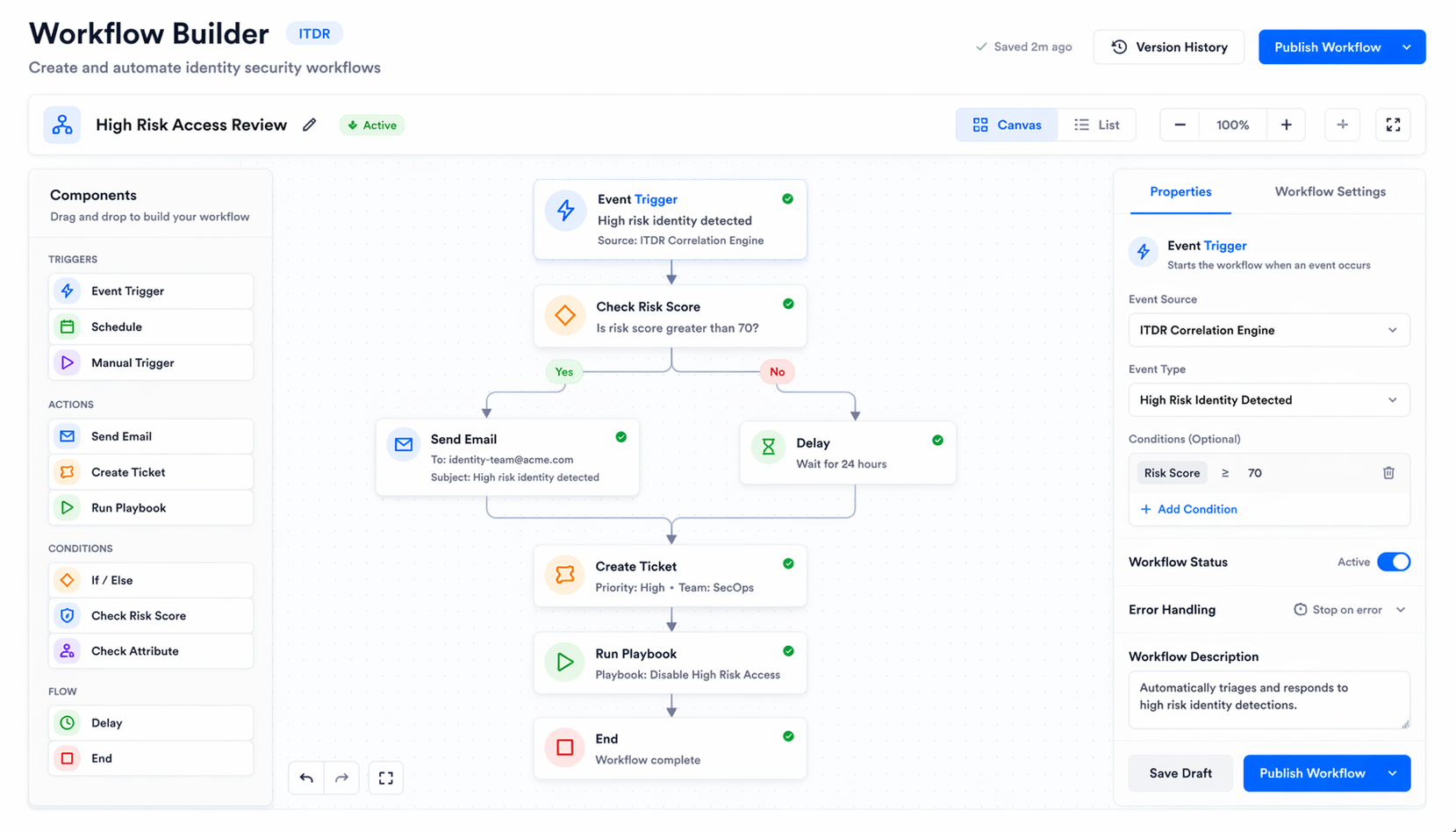
Other IGA runs reviews in a vacuum. Here, reviewers see active threat alerts before clicking approve.
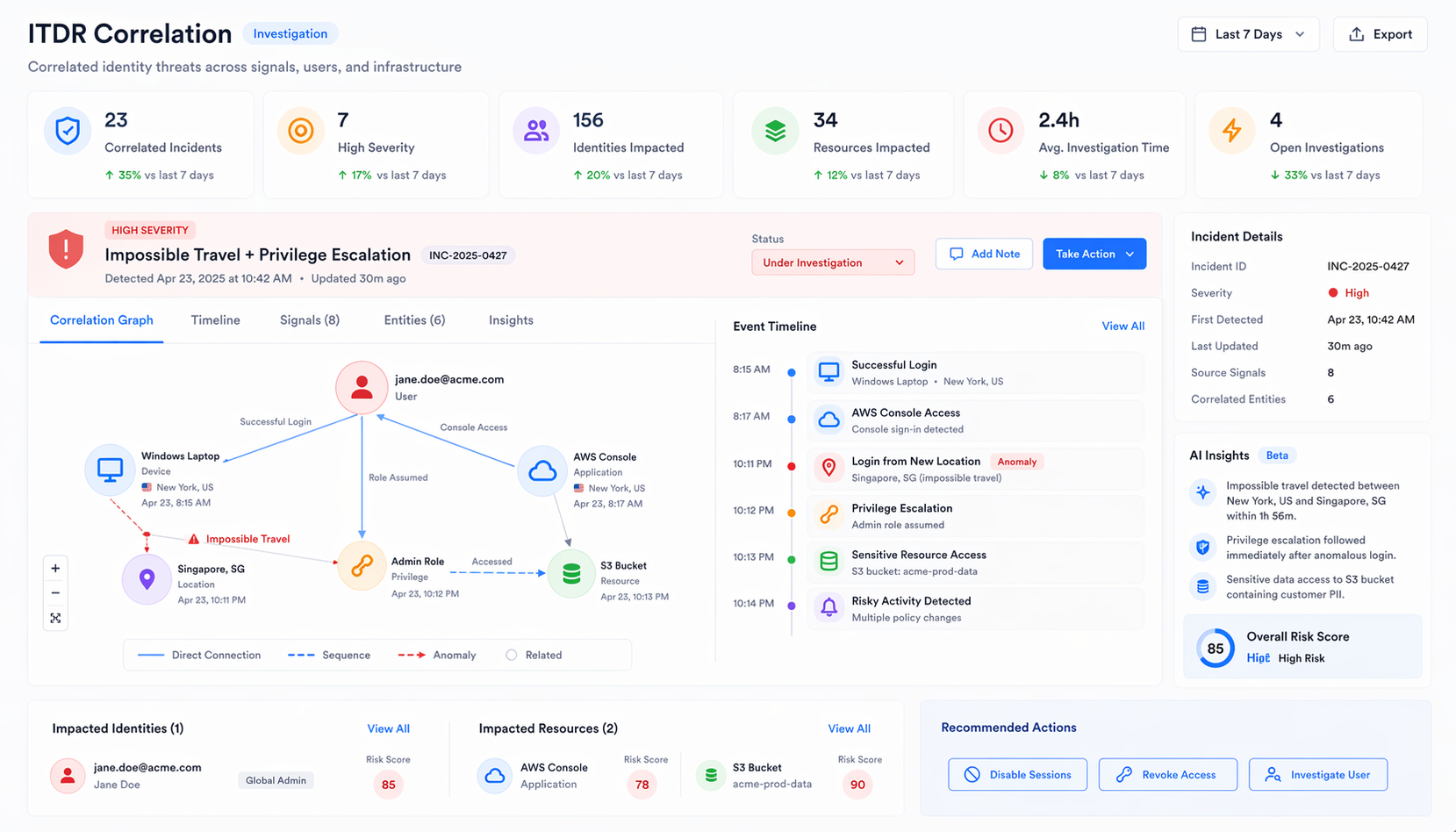
10,000 SIEM alerts become 3 investigations. Suspicious login, privilege escalation, OAuth grant - one chain, not three tickets.
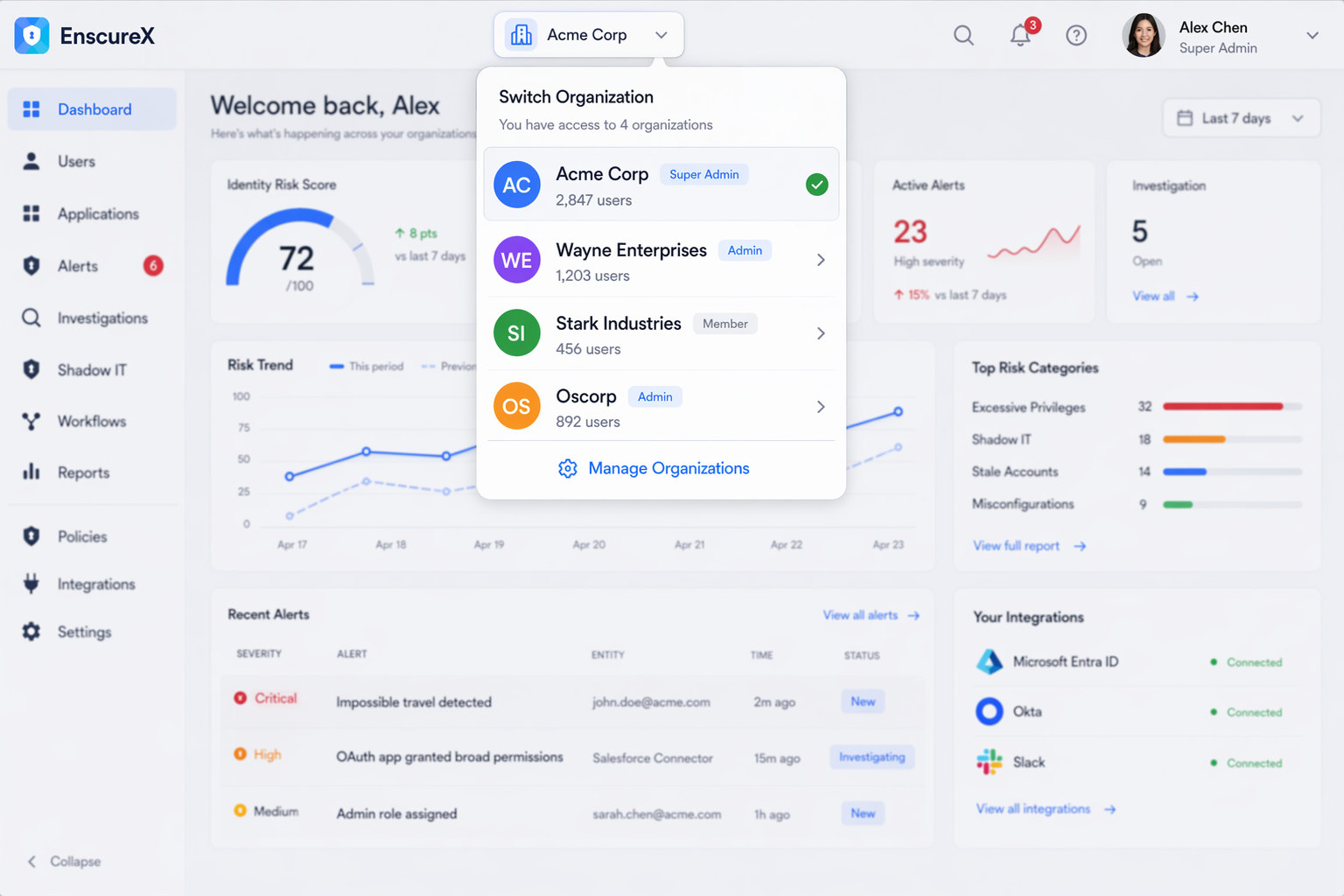
Data isolation per org. Role hierarchy per tenant. Independent config per customer. Architecture, not a feature flag.
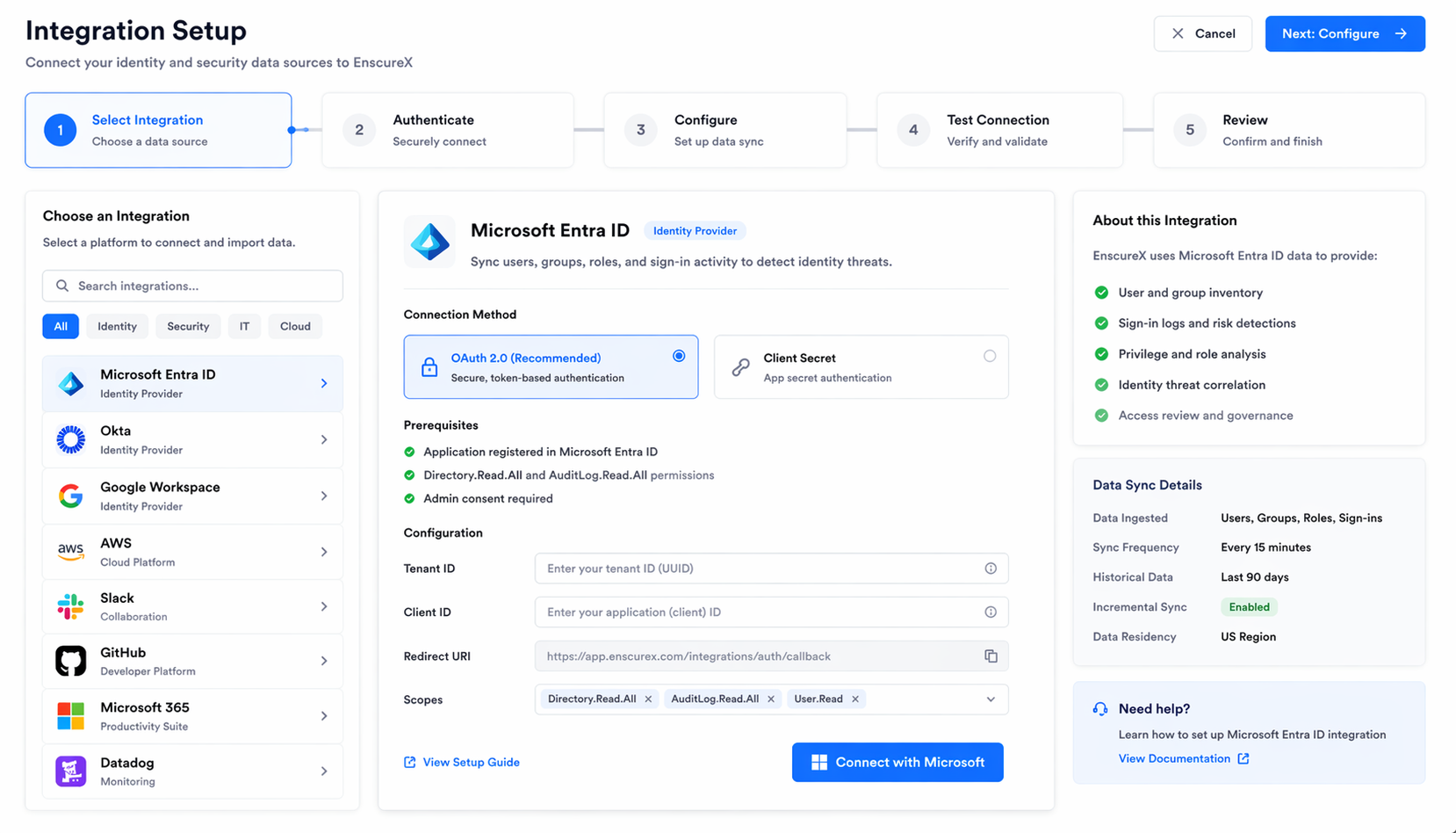
Connect Azure Entra ID, Okta, or Google Workspace. Every user, group, app, and sign-in event. Five minutes.
Shadow IT surfaces automatically. Reviews run on your schedule. Provisioning through workflows, not tickets.
Detection rules run 24/7. Correlation engine turns noise into investigations. Risk findings catch misconfigs first.
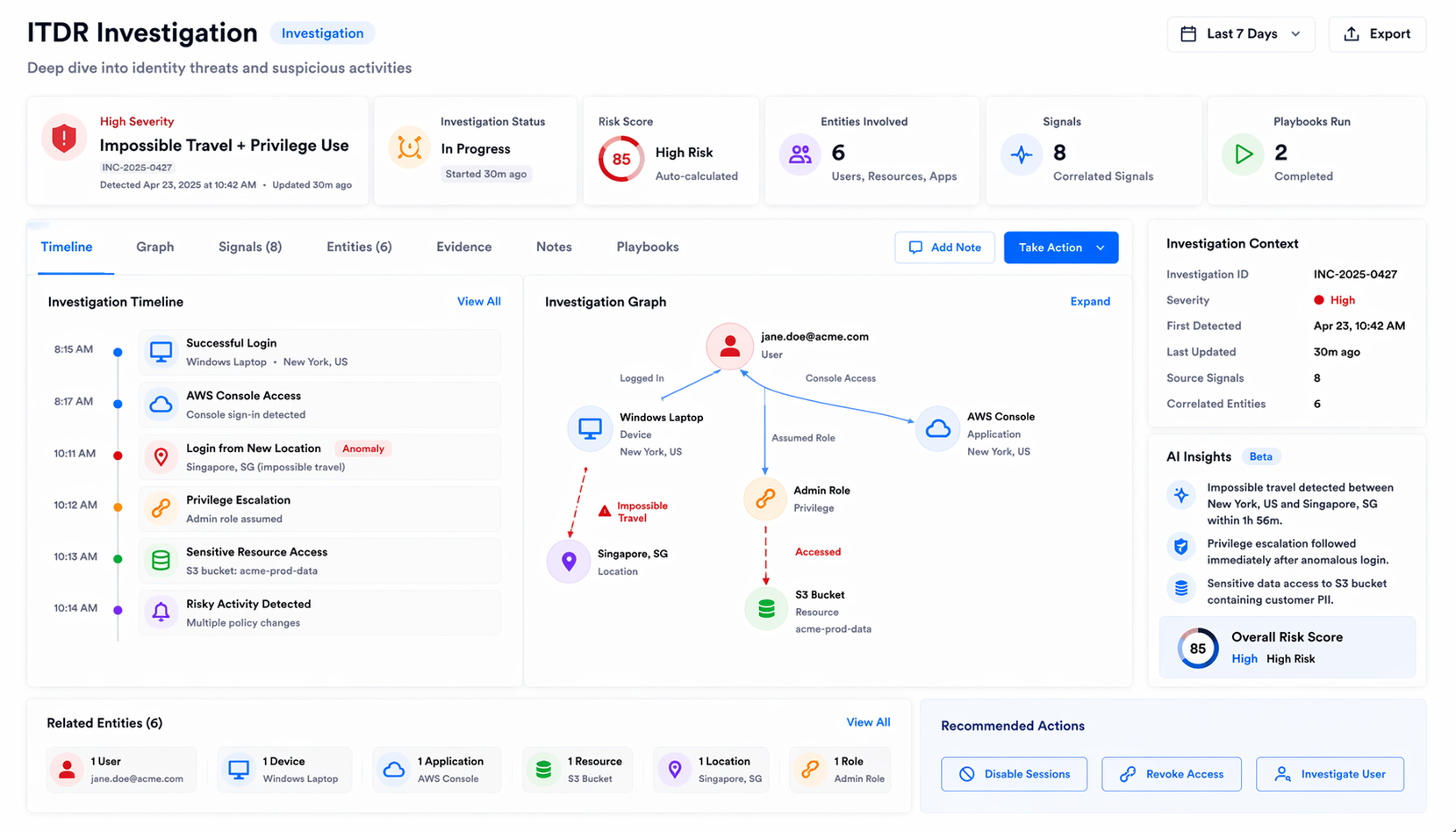
Impossible travel + password change + OAuth grant = one investigation
Unusual admin access detected in real time
Every OAuth grant mapped and risk-scored by scope
Flag dangerous service principal permissions automatically
User credentials checked against breach databases continuously
Timeline, correlated signals, AI summary. One screen.
Groups, apps, roles provisioned before day one
One trigger. All access revoked instantly.
Find unsanctioned apps with automated risk scoring
Track spend. Get renewal alerts. Stop surprises.
Real-time directory sync via Microsoft Graph API
Recurring certification campaigns. No spreadsheets.
365-day retention. Every change tracked with full context.
SOC 2, ISO 27001, NIST reports. Audit-ready.
Emergency access with audit trail. Auto-revoked after.
Define once. Workflows fire on governance events.
Identity providers, HR, cloud, dev tools, productivity, security, and finance.












































































JIT access. Session recording. Credential vaulting.
Multi-cloud misconfiguration detection. CIEM. Attack paths.
200+ frameworks. Automated evidence collection. Continuous monitoring.
Asset discovery. License optimization. Lifecycle tracking.
See what governance with threat detection looks like.